End-to-end IT infrastructure, advanced networking, and secure cybersecurity protocols tailored for modern enterprises.

Proactive monitoring, maintenance, and support to ensure your IT infrastructure runs smoothly 24/7.

Seamless network establishment across PAN India, ensuring secure, scalable networks tailored to your specific needs.

Top-tier solutions protecting your business from evolving threats. Customized measures keeping your data safe from cyberattacks.

Expert consulting to optimize your technology setup, delivering scalable and efficient systems for business growth.

Implementing reliable and secure surveillance systems to protect your office premises and physical assets.
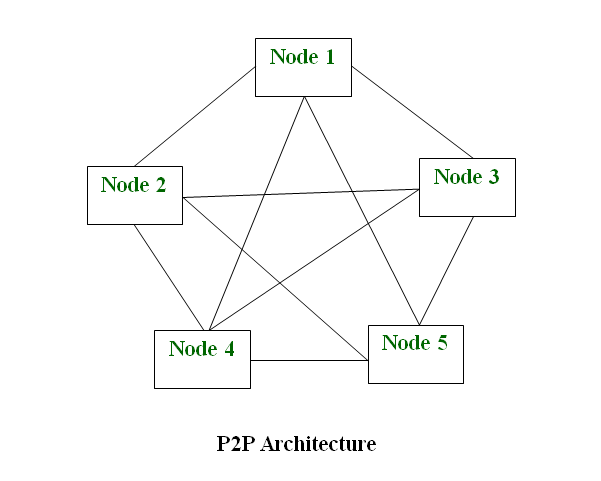
Specialized services for Network Design and Engineering, Network Layer Design, and Network-to-Network Interface.
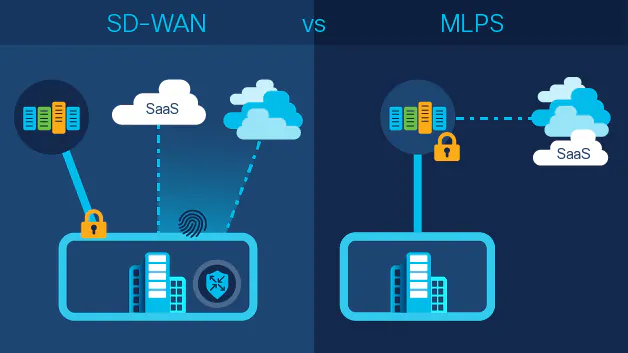
Implementing and managing modern networking solutions like SD-WAN and MPLS for highly optimized connectivity.

Designing and managing efficient data centers and optimizing automated business workflows for high productivity.
Implementing automation to streamline IT operations, reduce manual load, and improve efficiency for your business.

Configuring and managing network routing and switching protocols for optimal data flow and minimal latency.

Providing comprehensive cloud solutions, including secure migration, remote management, and cost optimization.

Designing and implementing reliable, high-density, and high-performance WiFi networks for enterprise environments.

Deploying robust, next-generation firewall configurations to protect your network border from unauthorized access.